Relevance of EWRA in day-to-day AML Compliance
Relevance of EWRA in day-to-day AML Compliance
The Anti-Money Laundering and Combating the Financing of Terrorism (AML/CFT) regulatory framework in UAE requires Designated Non-Financial Businesses and Professionals (DNFBPs) and Virtual Asset Service Providers (VASPs) to adopt a risk-based approach (RBA) to combat money laundering (ML) and financing of terrorism (TF), and proliferation financing (PF) risks.
As the regulatory frameworks for DNFBPs and VASPs in UAE require them to adopt RBA, conducting a Business Risk Assessment (BRA) or the Enterprise-wide Risk Assessment is necessary to identify, assess and determine the degree of risk posed to a regulated entity from the perpetrators of M/FT and PF.
Refer to our blog Checklist for Effective EWRA Documentation to understand the requisites for EWRA.
Here’s the list of uses of EWRA that regulated entities, such as DNFBPs and VASPs, can
1. Defining "Risk-centred" AML/CFT and CPF Policies and Procedures
Having conducted EWRA accurately helps regulated entities such as DNFBPs and VASPs to formulate AML/CFT and CPF policies and procedures that are tailored according to the risk findings.
Tailoring AML/CFT and CPF policies and procedures according to EWRA facilitates developing the compliance processes considering the risk weightage applied to various risk factors such as customers, geography, delivery channels and products or services.
Illustration: No two regulated entities operating in the same sector require the same set of AML/CFT and CPF policy and procedures. For example, two DNFBPs operating as jewellers can have distinct levels of risk posed by customers and geography due to factors such as:
- Region from where they source their raw materials, i.e., the gold bullion could differ. One may source it from the high-risk jurisdictions as defined by FATF, and the other may source it from a well-regulated and reputable jurisdiction with strong anti-financial crime regulations. Then, the degree of risk posed by the delivery channels used or the nature of the customer base differs, requiring respective jewellers to implement relevant AML/CFT and CPF measures.
- The resultant AML/CFT and CPF policy needs to be developed by keeping the core risk areas at the centre while developing procedures that help mitigate such risk effectively.
Drafting adequate and appropriate AML/CFT and CPF program requires the outcome of EWRA to determine the degree and extent of procedures to be taken to customise, supplement, and fortify AML/CFT and CPF efforts.
2. Foundation for developing Customer Risk Assessment methodology
Regulated entities need to conduct a business risk assessment to identify the proportion of various risk factors that contribute to the overall risk profile. This is then translated into a mechanism to derive the risk each customer poses to the business. A vicious circle – customer risk to business risk and overall business risk to risk from each customer.
A sound and effective CRA process for a regulated entity such as a DNFBP or VASP is integrated, aligned, and developed with the parameters used for the EWRA process.
Having access to EWRA findings facilitates regulated entities to formulate and develop CRA parameters, risk scoring methodology and overall program to customer risk assessment. CRA is the function of risk-weightage derived for each risk factors considered during the EWRA exercise.
Illustration: The outcome of the CRA exercise and subsequent customer risk profiling and scoring would differ for the same customer from one DNFBP to another. For example, the CRA outcome of one real estate agent to another real estate agent shall differ due to variations in degree, extent, and risk weightage assigned to various risk factors in the course of assessing the business risk.
- A customer, say, for example, Mr ABC for a real estate agent – Company A, may pose ‘low’ risk as identified post CRA as the majority of Company A’s customer base consists of high net-worth individuals and Mr ABC is also a high net worth individual, becoming homogenous with Company A’s existing and usual customer base.
- Contrastingly, the same customer, Mr ABC, for a real estate agent – Company B, may pose a ‘high’ ML/FT and PF risk, due to Company B’s customer base mostly consisting of lower and middle-income group clients, making Mr ABC as a customer with unusual profile.
- In both the above situations, the customer, Mr ABC, and the business sector for which he is a customer remained the same. However, distinguishing factors resulting in different risk scoring as ‘low’ or ‘high’ is the EWRA outcome (the overall business portfolio affects the regulated entity’s risk acceptance level). EWRA outcomes for both real estate agents, Company A and Company B differed because of the general business profile they have.
The above illustration emphasises how the use of EWRA outcome acts as a foundation on the basis of which, the CRA methodology is developed.
3. Fosters Optimal Resource Allocation with Risk-Based Approach
A Risk-Based Approach calls for implementing risk mitigation measures commensurate with the level and extent of risk faced.
The findings of EWRA facilitate a regulated entity such as a DNFBP or VASP to take a risk-based approach (RBA) while making resource allocation decisions, taking into account the following:
- Whether all the business activities of the regulated entity are covered by AML regulatory compliance or whether some of their activities are prone to risk requiring AML measures and the rest of the activities are not subject to AML compliance.
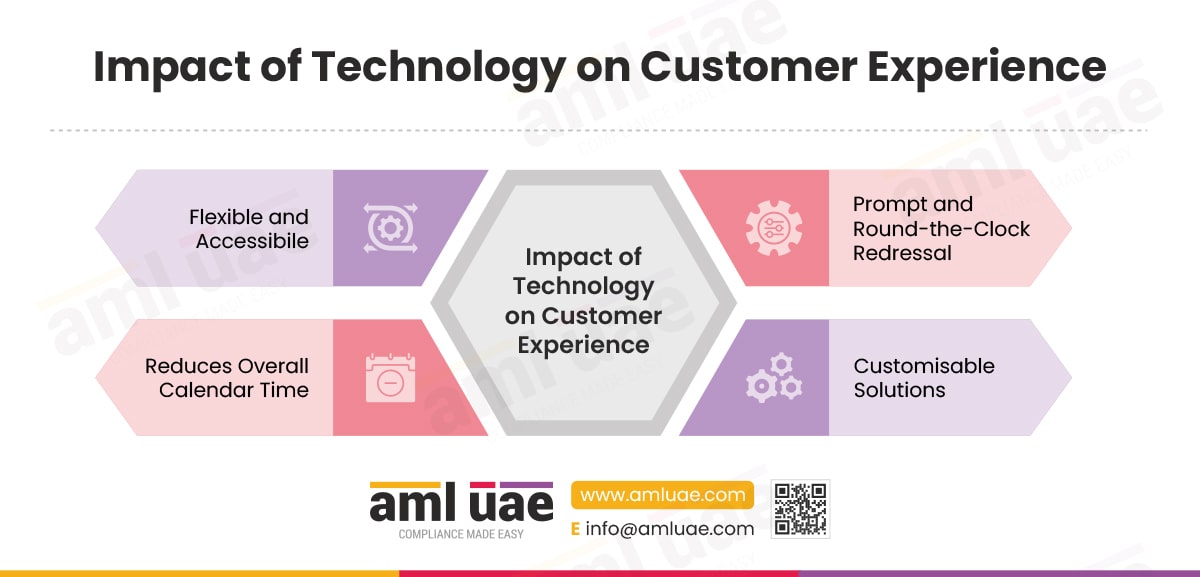
- The distributing the AML compliance tasks between human resources and advanced technological tools.
- Applying EDD measures only to high risk customers and not bothering low-risk customers.
- Whether the existing workforce is capable of absorbing the AML compliance workload, or whether new employees such as KYC Analysts, Screening Analysts need to be onboarded or whether the AML compliance obligation needs to be met through the assistance of AML experts or AML consultants.
Collection of the abovementioned information helps DNFBPs and VASPs to assess how resource-intensive the AML compliance for their organisation would be and take a risk-based decision while allocating funding and resources to mitigate ML/FT and PF risks effectively.
Illustration/ Use Case: Check out the EWRA and its alignment with the AML/CFT Policy for a TCSP.
4. Customising AML/CFT and CPF Training aligned with assessed risks
Upon conducting EWRA, a regulated entity can assess the level of control measures it needs to exercise for effective mitigation of ML/FT and PF risks.
Such mitigation measures require active involvement of the employees or personnel of the regulated entity.
Employees can be effective in mitigating ML/FT and PF risks only when they are adequately and appropriately trained in accordance with the typologies of ML/FT and PF risk specific to their employer’s assessed risks.
Depending on the EWRA findings and assessed risks, the regulated entity can identify in which specific area its personnel require training.
Illustration: One DNFBP, having high customer risk weightage in EWRA, would need to have its AML training planned with a special focus on customer onboarding measures such as customer due diligence (CDD), aligning with global sanctions lists, decoding sanctions screening results, how to deal with unaddressed matches during sanctions screening, customer onboarding and offboarding policy and practices, etc.
Whereas, another DNFBP, having low customer risk due to a homogenous customer mix and low number of customer turnover and repeat customers, needs to have AML training focused around the area like ongoing CDD and transaction monitoring.
Note: Role-Specific AML/CFT/CPF Compliance Training is necessary throughout the regulated entity to meet regulatory requirements of designing, conducting, and imparting AML/CFT and CPF training to employees. The EWRA findings facilitate tailoring and customising AML/CFT and CPF training on the basis of areas of business that are more vulnerable to ML/FT and PF than others.
5. Deploying ML/FT and PF Controls, sufficient to mitigate assessed risks
Utilizing EWRA findings helps in determining the baseline AML controls, such as whether there is a need to set up an in-house AML compliance department or whether managed KYC services can be used to mitigate assessed risks.
Determining the degree of and ways to apply CDD measures and exceptions to CDD, e.g., whether delayed verification of identity can be permitted and, if yes, under what circumstances.
Determining the process for obtaining user and beneficiary information for implementation of the FATF travel rule when dealing with virtual assets (VAs).
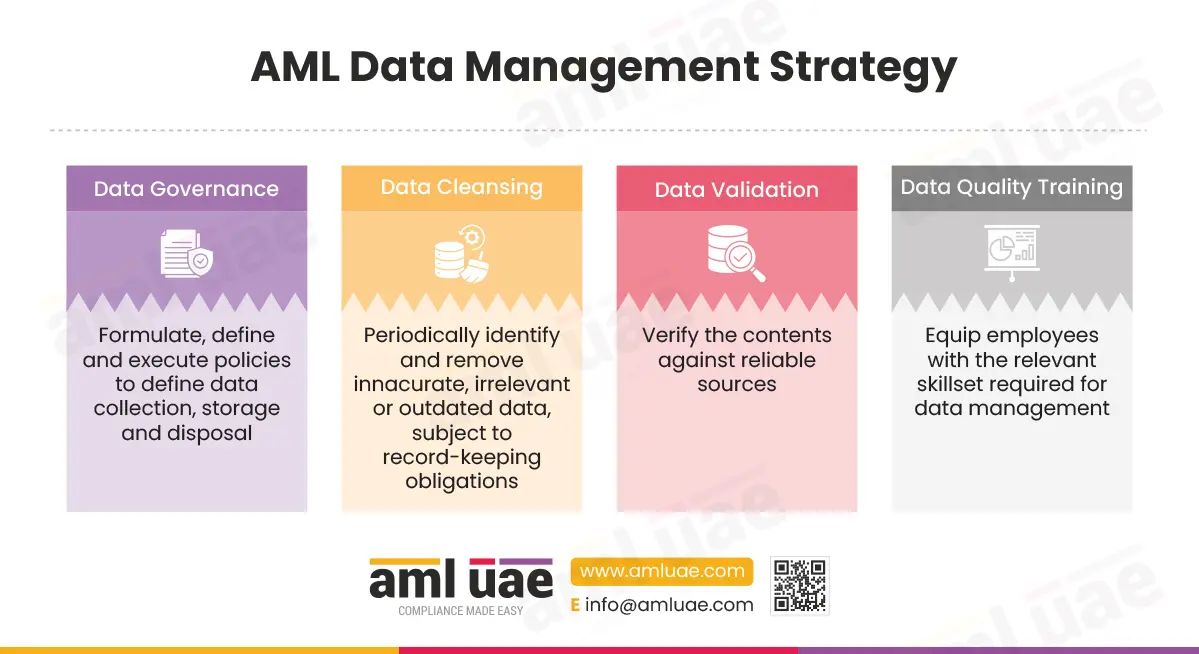
The findings of EWRA help regulated entities such as DNFBPs and VASPs to determine the type of AML solution required for fulfilling its AML compliance requirements.
- Whether switching from existing screening software is required or using the same one with fine-tuning would suffice.
- Whether automated AML software is suitable for the business, considering size, volume of transactions, and operations,
- Whether unified AML software solution is required or only process-specific AML software would be sufficient, such as:
- AML case management software
- KYC software
- Screening Software
- Transaction Monitoring Software
- Such selection must be made on the basis of sector and the various ML/FT and PF risk factors assessed.
- To be able to implement AML software for the AML compliance process, it is essential to understand the role of technology in AML compliance.
- Illustration: Implementing Cutting-Edge AML Software in the DNFBP Sector.
6. Contributes to overall AML governance (Frequency of AML Audit or internal AML reporting
The AML governance framework can be drafted only upon having EWRA findings in hand, giving the regulated entity a clear idea as to how the escalation workflows and allocation of responsibilities shall take place.
Allocating and determining the roles and responsibilities of AML compliance officer or Money Laundering Reporting Officer.
Defining the role of senior management in AML compliance process.
Determining the periodicity of getting an independent AML audit done (more frequent audits for a DNFBP whose EWRA outcome suggests high or medium net risk exposure, as compared to a DNFBP with low net risk exposure).
Illustration: Mastering STR Filing to Deter Financial Crimes for a DNFBP.
Illustration II: Assessing AML Control Effectiveness for an Audit Firm.
Conclusion
The exercise of conducting EWRA has multifold benefits. The process of EWRA is the starting point for determining what AML measures a DNFBP or VASP needs to take and what are the best-suited options for the fulfilment of AML compliance needs.