Pathik Shah
Last Updated: 12/22/2025
Protect your business with reliable and effective AML strategies with AML UAE.
Brief Overview of Virtual Asset Users
- Virtual Asset (VA) users are individuals or entities that owns, holds, trades, transfers, or stores digital assets such as cryptocurrencies, stablecoins, NFTs, or tokenized assets etc.
- The rapid growth of crypto and other virtual assets has increased regulatory focus on identifying, monitoring, and assessing VA user activity.
- Enhanced controls and tools must be adopted by Regulated entities to manage risks arising from pseudonymity, cross-border transfers, and decentralized ecosystems.
Understanding the Virtual Asset User in AML Compliance
Any person that owns, holds, transfers, trades, or stores virtual assets such as cryptocurrencies, stablecoins, or tokenized assets for personal or business purposes are virtual assets (VA) users. VA users are different from Virtual Asset Service Providers (VASPs) and intermediaries. VASPs facilitate exchange, custody, transfer, or issuance of virtual assets. The intermediaries are entities such as brokers or payment processors that facilitate transactions on behalf of users. In simple words, virtual assets users are the ones who enjoy the services of VASPs and intermediaries when dealing in virtual assets; they are the consumers of the services provided by VASPs and intermediaries.
In the UAE, VA users have become more relevant due to the rapid adoption of crypto platforms and supervision of virtual asset activities by Virtual Assets Regulatory Authority (VARA). While digital assets offer efficiency and innovation, they also increase AML/CFT risks manyfold, particularly where cross-border transfers, and decentralized structures are involved. UAE regulators expect institutions to understand VA user behavior as part of customer risk profiling, onboarding, and ongoing monitoring frameworks aligned with national AML/CFT obligations.
ML/FT Risks Associated with Virtual Asset Users
Virtual asset users pose elevated AML/CFT risks due to blockchain pseudonymity, which conceals the true identity and original source of the transaction. Layering and transaction obfuscation can also be conducted using privacy coins, mixers, tumblers, and peer-to-peer (P2P) transfers. VA users may also unknowingly or deliberately transact with sanctioned wallets, darknet marketplaces, fraud networks, or entities linked to high-risk jurisdictions. The speed and borderless nature of virtual asset transfers further enable rapid money laundering cycles while reducing the window for detection.
In the UAE, regulators monitor these risks more stringently as digital asset acceptance and acquisition increased in recent times. Financial institutions and VASPs are required to demonstrate effective risk identification, screening, and mitigation controls for VA transactions to meet regulatory expectations.
Key ML/TF and PF Typologies Involving Virtual Asset Users
Common typologies include wallet-to-wallet transfers with no identifiable economic purpose and rapid in-and-out crypto movements inconsistent with a user’s risk profile or declared source of funds. Virtual Assets such as NFTs, gaming tokens, and stablecoins are increasingly used for hidden value or ownership transfer. Cross-platform, cross-chain movements between exchanges, DeFi protocols, and non-custodial wallets, etc. are often used to exploit regulatory gaps and reduce traceability.
VASPs must have efficient and risk-based controls in place to identify such existing and evolving typologies through behavioral analysis, transaction monitoring, and Enhanced Due Diligence (EDD) for high-risk VA transfers. Early detection and prevention of these patterns is important for preventing misuse of virtual assets for money laundering, terrorist financing or other financial crimes.
UAE Regulatory Framework Governing Virtual Asset Users
Virtual asset user risks are addressed under, Federal Decree-Law No. 10 of 2025 and the Cabinet Resolution No. (134) of 2025 Concerning the Executive Regulations of Federal Decree-Law No. (10) of 2025 Concerning Combating Money Laundering, Terrorist Financing, and the Financing of the Proliferation of Weapons which impose AML/CFT obligations to VASPs and regulated entities. In UAE, VARA (Dubai) provides dedicated oversight, while the SCA (Mainland) and CBUAE establish expectations for VASPs operating across the mainland and financial sector.
VASPs must also comply with the Travel Rule, conduct wallet screening, and maintain originator/beneficiary information. Other than this, licensing, governance, and ongoing compliance obligations must be followed by exchanges, custodians, and brokers dealing with Virtual asset users. Regulators expect a documented, risk-based approach aligned with UAE AML/CFT standards. AML UAE provides an extensive guidance regarding Virtual asset AML compliance.
Customer Due Diligence for Virtual Asset Users
CDD for virtual asset users by VASPs must include identity verification, wallet ownership validation, and risk scoring based on transactional behavior. VA users should be screened against sanctions lists, PEP databases, and adverse media sources. Enhanced Due Diligence must be triggered, and escalation process be initiated where users demonstrate high-risk indicators, including high transactional volumes, use of privacy tools to disguise originator or beneficiary details, or extensive cross-border transfers.
Source of Funds/Wealth verification must also be conducted for higher-risk VA users, particularly during fiat-to-crypto or crypto-to-fiat conversions. Regulators expect VA user due diligence measures to be proportionate, documented, and equivalent in strength to traditional financial customer controls.
Transaction Monitoring and Blockchain Analytics
Blockchain analytics are essential for monitoring VA user activity and identifying suspicious wallet behavior. Key red flags include mixing services, chain hopping, unusual token swaps, and interactions with scam-linked or sanctioned addresses. Monitoring frameworks should assess transaction speed, size, frequency, and counterparties.
Integration with case management systems must be such that it allows timely investigation, escalation, and reporting of suspicious activity. AI-driven analytics further helps in detection of complex patterns and emerging typologies in the VA landscape. VASPs are expected to demonstrate effective, continuous monitoring of VA user transactions as part of their AML/CFT programs.
Common Compliance Gaps in Managing Virtual Asset Users
Frequent gaps mitigating AML compliance gaps include weak wallet risk classification, limited on-chain screening, and insufficient CDD for small or repetitive VA users. Many VASPs may have limited understanding of DeFi platforms, P2P networks, and non-custodial wallets.
Poor implementation of the Travel Rule, particularly non-disclosure of originator or beneficiary data remains a key regulatory concern in the UAE. AML UAE can assist the firms to address these gaps through ongoing risk assessments, control enhancements, and specialized staff training.
How AML UAE Supports VASPs and Financial Institutions Managing Virtual Asset Users
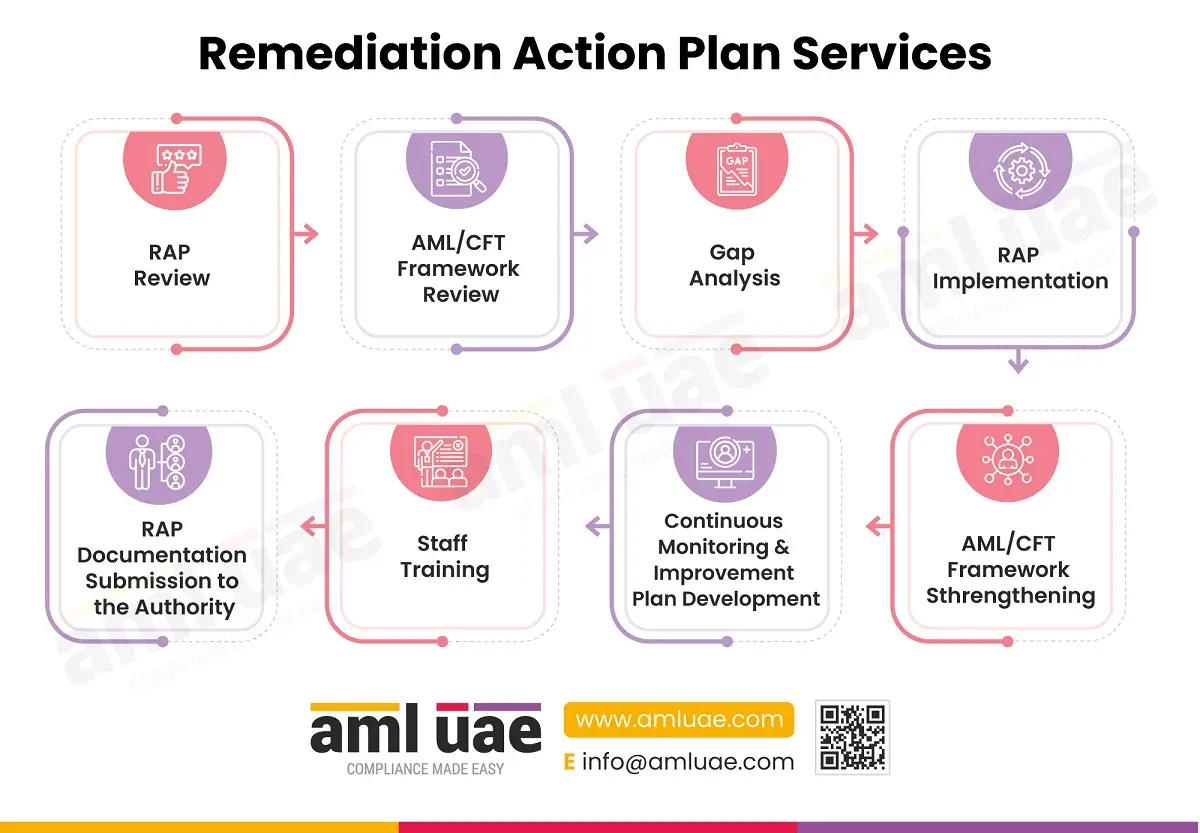
AML UAE Supports organizations with advisories on VA user screening, Travel Rule compliance, blockchain analytics, and transaction monitoring frameworks. It helps organizations transform their AML compliance game by providing gap assessments, remediation support, and targeted training to help institutions build robust, regulator-aligned virtual asset compliance programs.
Frequently Asked Questions
A virtual asset user is any individual or entity that owns, holds, transfers, trades, or stores digital assets, whose activity must be assessed and monitored for AML/CFT risks by Regulated entities.
Common red flags include use of privacy coins, high volume rapid in-and-out transactions, exposure to sanctioned or high-risk wallets, and cross-border transfers with no clear economic purpose.
KYC for VA users specifically requires identity and wallet verification, sanctions and PEP screening, risk scoring and profiling, and enhanced due diligence for high-risk users, in accordance with UAE AML/CFT regulations.
Our Timely and Accurate AML consulting Services
For your smooth journey towards your goals
Share via :
About the Author
Jyoti Maheshwari
CAMS, ACA
Jyoti has over 11 years of hands-on experience in regulatory compliance, policymaking, risk management, technology consultancy, and implementation. She holds vast experience with Anti-Money Laundering rules and regulations and helps companies deploy adequate mitigation measures and comply with legal requirements. Jyoti has been instrumental in optimizing business processes, documenting business requirements, preparing FRD, BRD, and SRS, and implementing IT solutions.

Reach Out to Jyoti