How the Tone from the Top Shapes Governance Aspect of AML/CFT Compliance
How the Tone from the Top Shapes Governance Aspect of AML/CFT Compliance
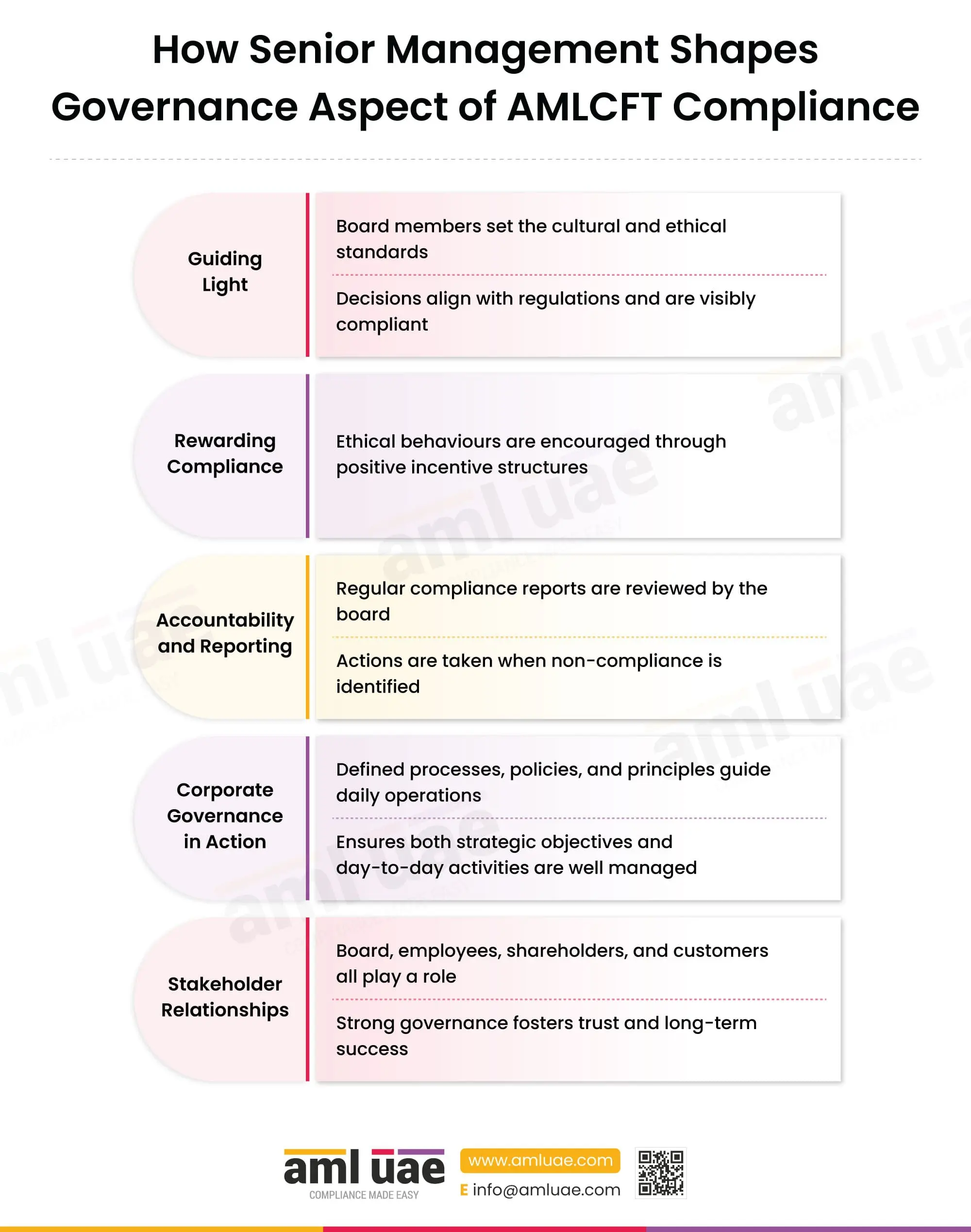
The tone from the top overlooks the establishment of strong AML/CFT Governance in an entity. Senior management helps implement a robust AML/CFT compliance culture. This infographic discusses in depth how the tone from the top shapes the governance aspect of AML/CFT Compliance by discussing the following aspects in detail:
- Guiding Light
- Rewarding Compliance
- Accountability and Reporting
- Corporate Governance in Action
- Stakeholder Relationship
Let us discuss the above-mentioned aspects in detail.
Guiding Light
Board members set cultural and ethical standards
Board members play a pivotal role in establishing the regulated entity’s cultural and ethical standards. They are responsible for setting the tone at the top, which is critical for fostering a strong compliance culture. This involves defining the entity’s risk appetite concerning money laundering and financing of terrorism (ML/FT) and ensuring the allocation of adequate resources to support AML/CFT compliance. Additionally, board members oversee and approve the entity’s overall AML/CFT program, ensuring its alignment with regulatory requirements and best practices.
Decisions align with regulations and are visibly compliant
The regulated entities consider the Enterprise-wide risk assessment (EWRA) for assessing the likelihood and impact of each risk factor upon an entity. This comprehensive evaluation aids in making informed, risk-based decisions and in formulating policies and procedures to manage and control ML/FT risks effectively. These decisions should align with the rules and regulations, demonstrating visible compliance. Adhering to regulatory standards not only enhances compliance but also strengthens the overall integrity of the entity.
Rewarding Compliance
Ethical behaviours are encouraged through positive incentive structures
The board can encourage ethical behaviour and reduce the cases of non-compliance by introducing some positive incentive structures. The incentive structure can include some special types of rewards and recognition like cash prizes or letters of appreciation. The culture of incentive is a way of recognizing the efforts of employees, which encourages them to continue to demonstrate the desired behaviour.
Accountability and Reporting
Regular compliance reports are reviewed by the board
The compliance officer is responsible for reporting compliance reports indicating identified risks to the board to ensure the board is fully aware of the entity’s affairs, enabling them to make informed and appropriate decisions. These reports should include updates on changes to laws and regulations that require immediate action, ensuring the entity remains compliant and responsive to legal requirements.
In addition to compliance reports, audit reports should also be presented to board members, providing an independent assessment of the entity’s policies, procedures, and controls for comprehensive decision-making.
Actions are taken when non-compliance is identified
After reviewing the compliance and audit reports, if the board identifies any deficiencies related to AML/CFT, it is essential for them to take necessary actions to address these issues. For instance, if senior management discovers a deficiency in Know Your Customer (KYC) processes due to outdated software, they should develop a corrective action plan that includes deploying updated software to rectify the situation.
Furthermore, it is crucial for management to stay informed about the follow-up on the implementation of these corrective measures, ensuring that all actions taken effectively mitigate the identified deficiencies and enhance compliance.
Corporate Governance in Action
Defined processes, policies, and principles guide daily operations
EWRA helps a regulated entity determine the degree and type of risk posed to it by the ML/FT perpetrators. Based on the assessment, the entity formulates policies, procedures, and control measures to mitigate these risks effectively.
These policies and procedures are then integrated into the entity’s daily operations, serving as a framework to guide activities, ensure compliance, and reduce risks. This structured approach enables the entity to proactively manage risks while maintaining efficiency and adherence to regulatory requirements.
Ensures both strategic objectives and day-to-day activities are well managed
EWRA helps formulate policies, procedures, and control measures that mitigate risks while aligning with the entity’s broader strategic goals. By integrating these measures into day-to-day operations, the entity establishes a structured framework that not only guides day-to-day activities but also ensures compliance with regulatory requirements and supports decision-making at all levels.
This approach helps the entity proactively manage risks, optimize resource allocation, and maintain efficiency while achieving strategic goals. It ensures seamless integration between strategic objectives and daily operations for cohesive and effective management.
Stakeholder Relationships
Board, employees, shareholders, and customers all play a role
The board and senior management are responsible for the implementation of the AML/CFT program in the entity. The senior management sets the tone from the top for building strong AML/CFT governance. Employees are often the first line of business and play an important role in identifying any red flags. The board and employees together form a strong governance system, which ultimately boosts the confidence and trust of the customers and the stakeholders.
Strong governance fosters trust and long-term success:
Strong governance in an entity builds trust in the customers as it reduces the chances of ML/TF risks. It even improves the stability ratio of customers. For example, customers build long-term relationships, which help attain long-term success in a regulated entity.
Tone From the Top Shapes Governance Structure - An Overview
A strong governance structure is driven by the commitment and leadership of the board and senior management. They are responsible for shaping the AML/CFT framework by demonstrating accountability, ensuring compliance, and articulating clear expectations for all staff. Their active engagement ensures the effective implementation of policies, procedures, and controls, aligning daily operations with regulatory standards and the entity’s objectives.
Related Posts
Confused with how to mitigate ML, FT, and PF risks within your Regulated Entity?